What is Zero Trust Security: The New Standard of Defense
In the early days of the internet, cybersecurity worked like a medieval castle: build a thick wall (the perimeter) and trust everyone inside. But in 2026, the walls have crumbled. With remote work, cloud migration, and sophisticated AI-driven hacks, the “castle” no longer has a single entrance. This is where the concept of What is Zero Trust Security becomes vital—it is a paradigm shift that assumes threats are already inside the network.
Every day, thousands of businesses fall victim to breaches because they trusted a “verified” user too much. Zero Trust eliminates this vulnerability by replacing implicit trust with continuous verification. Whether you are a small business owner or an IT professional, understanding this framework is the only way to ensure your data remains uncompromised in an increasingly hostile digital landscape.
2. The Core Philosophy: Never Trust, Always Verify
The fundamental answer to What is Zero Trust Security lies in its name: zero inherent trust. Traditional security models focus on defending the perimeter, but once an attacker bypasses the firewall, they have “lateral movement” to steal everything. Zero Trust prevents this by requiring every user, device, and application to be authenticated and authorized every single time they request access to a resource.
Modern organizations often look toward high-level frameworks like dod cloud computing security to understand how to protect massive data sets in decentralized environments. By adopting these stringent standards, companies can ensure that identity—not location—becomes the new security perimeter. In this model, it doesn’t matter if you are sitting in the office or a coffee shop; the security requirements remain equally strict.
3. How Zero Trust Operates in Real-World Scenarios
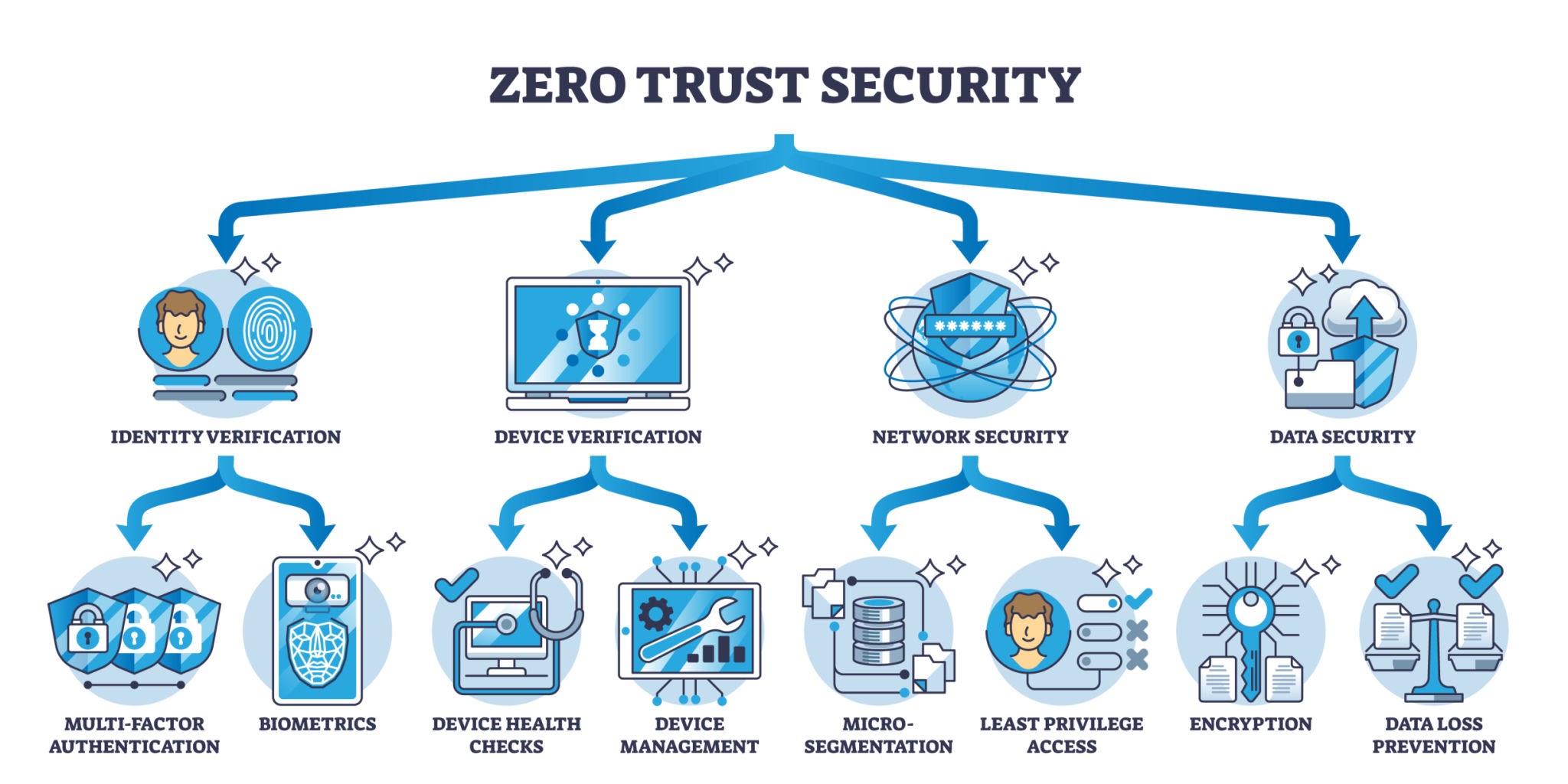
To implement Zero Trust, organizations must integrate several moving parts, including Multi-Factor Authentication (MFA), Micro-segmentation, and Endpoint Security. It is not a single product you buy, but a strategy you build. Many businesses find that partnering with cyber security services is the most efficient way to audit their current infrastructure and transition to a “Zero Trust” posture without disrupting daily operations.
A key component of What is Zero Trust Security is Micro-segmentation. Imagine your network is a submarine; if one compartment floods, you seal the doors to save the rest of the ship. Micro-segmentation does exactly this with your data, breaking the network into small, isolated zones so that if a hacker steals one password, they are stuck in a tiny “room” with nowhere else to go.
4. Comparison: Traditional Security vs. Zero Trust
Understanding the technical shift requires a side-by-side look at how these models handle a typical user request.
| Feature | Traditional Security (Perimeter) | Zero Trust Security (Holistic) |
| Trust Model | Implicit trust for anyone inside. | Zero trust; verify everyone always. |
| Primary Focus | Defending the “walls” (Firewalls). | Defending the “assets” (Data/Identity). |
| Lateral Movement | High (Hackers can move freely). | Low (Blocked by micro-segmentation). |
| User Experience | One-time login (VPN). | Continuous, adaptive authentication. |
| Threat Assumption | Threats are outside. | Threats are both inside and outside. |
5. The Three Main Pillars of Zero Trust
When exploring What is Zero Trust Security, experts generally point to three non-negotiable pillars that sustain the framework:
- Continuous Verification: The system constantly checks user identity, device health, and location throughout the entire session, not just at login.
- Limit Blast Radius: By using micro-segmentation, you ensure that a single compromised account cannot bring down the entire organization.
- Automated Context Collection: Using AI to analyze logs and behavior in real-time. If a user usually logs in from New York but suddenly appears in Eastern Europe, the system automatically blocks access.
6. Pros and Cons of Zero Trust Implementation
Is Zero Trust the right fit for everyone? Let’s look at it objectively.
Pros:
- Superior Protection: Drastically reduces the risk of data breaches and internal theft.
- Regulatory Compliance: Meets the strict requirements of GDPR, HIPAA, and federal standards.
- Visibility: Provides a crystal-clear view of who is doing what on your network at all times.
Cons:
- Implementation Time: It takes months or even years to fully transition a legacy network.
- Cost: Requires investment in new software, identity management tools, and expert consulting.
- Management Burden: IT teams must manage complex access policies for every single user role.
7. Expert Strategy: 4 Steps to Start Your Zero Trust Journey
If you are ready to move beyond just asking What is Zero Trust Security and want to start building it, follow this expert roadmap:
- Identify Your “Protect Surface”: You can’t protect everything at once. Identify your most “Crown Jewel” data (customer records, intellectual property) and build your Zero Trust zone there first.
- Map Transaction Flows: Understand how your data moves. Who accesses it? From where? This documentation is vital for setting accurate access policies.
- Implement MFA Everywhere: This is the quickest win. Multi-Factor Authentication stops 99% of bulk credential attacks. No Zero Trust environment can exist without it.
- Monitor and Loop: Zero Trust is not a “set and forget” system. Use automated tools to monitor behavior and adjust your policies as your business grows.
Verdict (Conclusion)
In conclusion, What is Zero Trust Security is more than just a buzzword; it is a necessary evolution in a world where data is the most valuable currency. By assuming that a breach is inevitable and verifying every single request, you don’t just protect your servers—anda protect your company’s reputation and future.
The Verdict: While the transition to Zero Trust requires significant effort and cultural shift within an organization, the cost of not doing it is far higher. In 2026, the question is no longer “if” you should implement Zero Trust, but how fast you can get it done. Security through obscurity is dead; security through verification is the only way forward.
FAQ: Common Questions About Zero Trust
- Is Zero Trust the same as a VPN?
No. A VPN creates a tunnel into a network and often grants too much trust once the user is inside. Zero Trust applies security at the individual application and data level, regardless of how you are connected.
- Does Zero Trust slow down employee productivity?
Not necessarily. Modern Zero Trust uses “Adaptive Authentication,” which only asks for extra verification if it detects something unusual (like a new device or a strange location). Most of the time, it is invisible to the user.
- Is Zero Trust only for large corporations?
No. Small businesses are often the biggest targets because they have weaker defenses. Many cloud providers now offer Zero Trust tools that are affordable for small teams.
- Can I buy Zero Trust in a box?
No. You can buy tools that enable Zero Trust, but the framework itself is a combination of policy, technology, and organizational culture.
