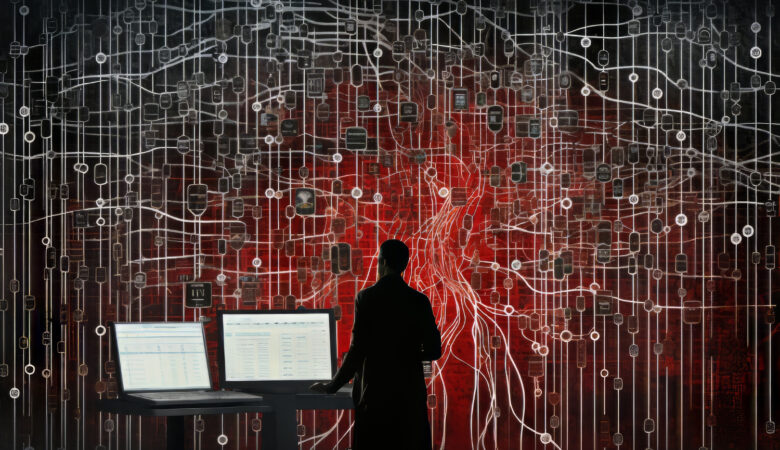
Outbreak Threat Map: Real-Time Global Disease Tracking You Can Trust
In today’s fast-evolving global health landscape, having rapid and reliable information is becoming increasingly crucial. As outbreaks can escalate within hours, individuals and organizations now rely heavily on an Outbreak Threat Map to monitor disease spread in real time. This tool offers immediate insights into how infectious threats evolve, helping users respond faster and more […]